2020. november 2., hétfő
google maps
https://www.str8-creative.co/product/1500-gmaps-citations/
thanks
Cordelia Paramo
2020. október 3., szombat
google maps
https://www.str8-creative.co/product/1500-gmaps-citations/
thanks
Larraine Cavallaro
2020. szeptember 22., kedd
HIDDEN GEMS - TOP 10 FORGETTEN FMV ADVENTURES
I'm back from a little holiday with another TOP 10 list! This time we're looking at the oft-maligned FMV adventure, complete with over-the-top acting and CD count! Not all of them deserve the bad reputation associated with the genre so I've collated some of the absolute best. Don't expect the revered likes of Gabriel Knight or The 7th Guest which are easily available to buy online. These are the forgotten gems that no-one seems to talk about anymore (if they ever did).
There's even a number of games not previously featured on the site (including QUANTUM GATE and THE CASSANDRA GALLERIES), so go check them out too!
Read more »
2020. szeptember 21., hétfő
Camouflaging The Imperial Guard Armoured Company
Not many updates but I've been slogging through the camouflage on the Armoured Company these past weeks. The base colors and shading are done, I'm now onto tidying. That should finish up this week and hopefully I can start on the highlights.

The green and tan each get a base, wash, neaten up, and two highlights. The black and metal get a wash and a highlight or two, depending on how they look.



I also painted this guy up over the course of a couple hours this week. He's a battle wizard from my last Kickstarter. He's meant to be a gold wizard/alchemist.


2020. szeptember 12., szombat
28Mm Modern Roads For The Sweeney And Beyond
CrossCode Review (NSW)
Title: CrossCode
Developer: Radical Fish Games
Publisher: Deck 13
Genre: Action, RPG
Price: $19.99
Also Available On: Steam, XB1
CrossCode makes no bones about its conceit. In fact, it trumpets its willingness to straddle seemingly incongruous situations. As a single-player role-playing game set within a massive multiplayer online RPG, it has players control Lea, an avatar who has lost both her memory and her voice, in an effort to solve the mysteries behind the development. And, what's more, she gets to mingle in the physical world as well. Thusly, two stories in two settings get intertwined on the way to the denouement.
Significantly, CrossCode makes Lea's progress within the CrossWorlds MMORPG run just about like any other player's character in real life. She's a Spheromancer with the capacity to launch both ranged and close-quarter attacks during inevitable combat phases. There's likewise a large portion of interaction with other characters, including with some slated to join in exploration, as well as a fair amount of crafting and farming in order to raise attributes to the levels required to take the measure of opponents in battle. Parenthetically, skill trees are extensive and can open up more opportunities, particularly chain attacks, in this regard.
Simply put, CrossCode gives off a decidedly MMORPG vibe without players actually needing to go online. And, creditably, it proves to be just as deep and as populated, not to mention as aesthetically and aurally pleasing as the best ones in the industry; the 16-bit art style complements the throwback music, adding to the lure and allure of the gameplay. If there are any negatives, they're in the frame rate drops when the screen gets busy, and in the audio glitches that occasionally crop up.
On the whole, though, CrossCode proves to be worth its $19.99 price tag as a well-made port of the crowdfunded release on the personal computer. With progressively challenging puzzles through seven themed dungeons, it's a satisfying 50-hour romp that gives off a Zelda-esque vibe in an MMORPG environment. Sweet.
THE GOOD
- Solid gameplay
- Balanced and fair combat mechanics
- Visually and aurally pleasing
THE BAD
- Populated screens lead to frame drops
- Audio glitches evident on occasion
- Side quests can be repetitive
- Grinding required
2020. szeptember 5., szombat
google maps
https://www.str8-creative.co/product/1500-gmaps-citations/
thanks
Hortense Guinan
2020. szeptember 4., péntek
Super Adventures With The Xbox Game Pass, Part 3
But I'm doing it anyway because I want to show some games off and I'm hoping someone reading these will discover something new they end up playing and loving, even if I didn't love it myself.
You can find part 1 here: Part 1.
And part 2 is here: Part 2.
The final part is coming tomorrow!
Read on »
2020. augusztus 30., vasárnap
DOS (Denial Of Service) Attack Tutorial Ping Of Death ;DDOS
What is DoS Attack?
DOS is an attack used to deny legitimate users access to a resource such as accessing a website, network, emails, etc. or making it extremely slow. DoS is the acronym for Denial of Service. This type of attack is usually implemented by hitting the target resource such as a web server with too many requests at the same time. This results in the server failing to respond to all the requests. The effect of this can either be crashing the servers or slowing them down.
Cutting off some business from the internet can lead to significant loss of business or money. The internet and computer networks power a lot of businesses. Some organizations such as payment gateways, e-commerce sites entirely depend on the internet to do business.
In this tutorial, we will introduce you to what denial of service attack is, how it is performed and how you can protect against such attacks.
Topics covered in this tutorial
- Types of Dos Attacks
- How DoS attacks work
- DoS attack tools
- DoS Protection: Prevent an attack
- Hacking Activity: Ping of Death
- Hacking Activity: Launch a DOS attack
Types of Dos Attacks
There are two types of Dos attacks namely;
- DoS– this type of attack is performed by a single host
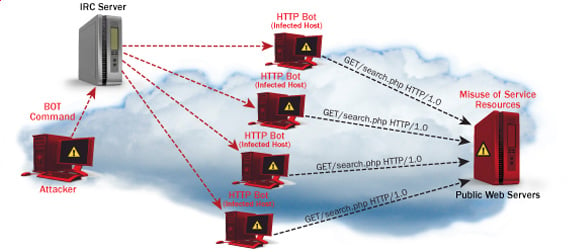
- Distributed DoS– this type of attack is performed by a number of compromised machines that all target the same victim. It floods the network with data packets.
How DoS attacks work
Let's look at how DoS attacks are performed and the techniques used. We will look at five common types of attacks.
Ping of Death
The ping command is usually used to test the availability of a network resource. It works by sending small data packets to the network resource. The ping of death takes advantage of this and sends data packets above the maximum limit (65,536 bytes) that TCP/IP allows. TCP/IP fragmentation breaks the packets into small chunks that are sent to the server. Since the sent data packages are larger than what the server can handle, the server can freeze, reboot, or crash.
Smurf
This type of attack uses large amounts of Internet Control Message Protocol (ICMP) ping traffic target at an Internet Broadcast Address. The reply IP address is spoofed to that of the intended victim. All the replies are sent to the victim instead of the IP used for the pings. Since a single Internet Broadcast Address can support a maximum of 255 hosts, a smurf attack amplifies a single ping 255 times. The effect of this is slowing down the network to a point where it is impossible to use it.
Buffer overflow
A buffer is a temporal storage location in RAM that is used to hold data so that the CPU can manipulate it before writing it back to the disc. Buffers have a size limit. This type of attack loads the buffer with more data that it can hold. This causes the buffer to overflow and corrupt the data it holds. An example of a buffer overflow is sending emails with file names that have 256 characters.
Teardrop
This type of attack uses larger data packets. TCP/IP breaks them into fragments that are assembled on the receiving host. The attacker manipulates the packets as they are sent so that they overlap each other. This can cause the intended victim to crash as it tries to re-assemble the packets.
SYN attack
SYN is a short form for Synchronize. This type of attack takes advantage of the three-way handshake to establish communication using TCP. SYN attack works by flooding the victim with incomplete SYN messages. This causes the victim machine to allocate memory resources that are never used and deny access to legitimate users.
DoS attack tools
The following are some of the tools that can be used to perform DoS attacks.
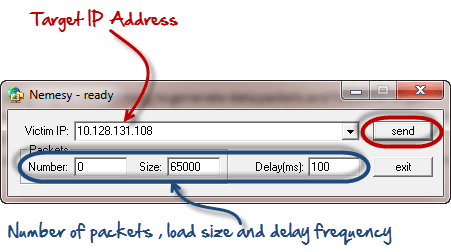
- Nemesy– this tool can be used to generate random packets. It works on windows. This tool can be downloaded from http://packetstormsecurity.com/files/25599/nemesy13.zip.html . Due to the nature of the program, if you have an antivirus, it will most likely be detected as a virus.
- Land and LaTierra– this tool can be used for IP spoofing and opening TCP connections
- Blast– this tool can be downloaded from http://www.opencomm.co.uk/products/blast/features.php
- Panther- this tool can be used to flood a victim's network with UDP packets.
- Botnets– these are multitudes of compromised computers on the Internet that can be used to perform a distributed denial of service attack.
DoS Protection: Prevent an attack
An organization can adopt the following policy to protect itself against Denial of Service attacks.
- Attacks such as SYN flooding take advantage of bugs in the operating system. Installing security patches can help reduce the chances of such attacks.
- Intrusion detection systems can also be used to identify and even stop illegal activities
- Firewalls can be used to stop simple DoS attacks by blocking all traffic coming from an attacker by identifying his IP.
- Routers can be configured via the Access Control List to limit access to the network and drop suspected illegal traffic.
Hacking Activity: Ping of Death
We will assume you are using Windows for this exercise. We will also assume that you have at least two computers that are on the same network. DOS attacks are illegal on networks that you are not authorized to do so. This is why you will need to setup your own network for this exercise.
Open the command prompt on the target computer
Enter the command ipconfig. You will get results similar to the ones shown below
For this example, we are using Mobile Broadband connection details. Take note of the IP address. Note: for this example to be more effective, and you must use a LAN network.
Switch to the computer that you want to use for the attack and open the command prompt
We will ping our victim computer with infinite data packets of 65500
Enter the following command
ping 10.128.131.108 –t |65500
HERE,
- "ping" sends the data packets to the victim
- "10.128.131.108" is the IP address of the victim
- "-t" means the data packets should be sent until the program is stopped
- "-l" specifies the data load to be sent to the victim
You will get results similar to the ones shown below
Flooding the target computer with data packets doesn't have much effect on the victim. In order for the attack to be more effective, you should attack the target computer with pings from more than one computer.
The above attack can be used to attacker routers, web servers etc.
If you want to see the effects of the attack on the target computer, you can open the task manager and view the network activities.
- Right click on the taskbar
- Select start task manager
- Click on the network tab
- You will get results similar to the following
If the attack is successful, you should be able to see increased network activities.
Hacking Activity: Launch a DOS attack
In this practical scenario, we are going to use Nemesy to generate data packets and flood the target computer, router or server.
As stated above, Nemesy will be detected as an illegal program by your anti-virus. You will have to disable the anti-virus for this exercise.
- Download Nemesy from http://packetstormsecurity.com/files/25599/nemesy13.zip.html
- Unzip it and run the program Nemesy.exe
- You will get the following interface
Enter the target IP address, in this example; we have used the target IP we used in the above example.
HERE,
- 0 as the number of packets means infinity. You can set it to the desired number if you do not want to send, infinity data packets
- The size field specifies the data bytes to be sent and the delay specifies the time interval in milliseconds.
Click on send button
You should be able to see the following results
The title bar will show you the number of packets sent
Click on halt button to stop the program from sending data packets.
You can monitor the task manager of the target computer to see the network activities.
Summary
- A denial of service attack's intent is to deny legitimate users access to a resource such as a network, server etc.
- There are two types of attacks, denial of service and distributed denial of service.
- A denial of service attack can be carried out using SYN Flooding, Ping of Death, Teardrop, Smurf or buffer overflow
- Security patches for operating systems, router configuration, firewalls and intrusion detection systems can be used to protect against denial of service attacks.
Related articles
- Hacker Tools Windows
- Hacker Tool Kit
- Hack Tools For Games
- Hacking Tools Usb
- Computer Hacker
- Top Pentest Tools
- Pentest Recon Tools
- Bluetooth Hacking Tools Kali
- Pentest Tools Nmap
- Physical Pentest Tools
- Pentest Tools Bluekeep
- Nsa Hacker Tools
- Hacker Tools Windows
- Hacker Tools Linux
- Hacker Tools Free Download
- Hacker Search Tools
- Hacking Tools 2020
- What Is Hacking Tools
- Underground Hacker Sites
- Hacking Tools For Mac
- Hacking Tools For Games
- Hack Tools
- How To Install Pentest Tools In Ubuntu
- Hacking Tools For Mac
- Hacker Tools Linux
- Nsa Hack Tools
- Hak5 Tools
- Hack Website Online Tool
- Hack Apps
- Hacks And Tools
- Hacking Tools Usb
- Hacking Tools For Pc
- Blackhat Hacker Tools
- Hacking Tools Kit
- Hack Tool Apk
- Hacker Tools For Mac
- Hacking Tools Github
- Hacking Tools Name
- How To Make Hacking Tools
- Hack Tools For Mac
- Hack Tools Github
- World No 1 Hacker Software
- Hack Tools For Pc
- Pentest Tools Download
- Hacking Tools Mac
- Hacker Techniques Tools And Incident Handling
- Hacking Tools Github
- Hacking Tools Usb
- Hack Tools For Mac
- Hacker Tools For Pc
- Hacker Tools List
- Hacker Tool Kit
- Hack Tools Online
- Game Hacking
- Github Hacking Tools
- Pentest Tools For Ubuntu
- Free Pentest Tools For Windows
- Pentest Tools Download
- Hacking Tools Mac
- Hacking Tools Windows
- Hack Tools For Ubuntu
- Hacking Tools 2019
- Hacking Tools Download
- Github Hacking Tools
- Ethical Hacker Tools
- Hacker Tools 2019
- What Are Hacking Tools
- Hacker Tools List
- Hacking Tools For Windows
- Pentest Tools Url Fuzzer
- Pentest Automation Tools
- Hacker Tools Free
- Hacking Tools Name
- Hacker Search Tools
- Pentest Tools Review
- Top Pentest Tools
- Hacker Tools For Mac
- Hacking Tools For Beginners
- How To Install Pentest Tools In Ubuntu
- Pentest Tools For Mac
- Hack Tools 2019
- Hacker Tools For Pc
- Pentest Tools List
- Hack Tools For Windows
- Hack Website Online Tool
- Beginner Hacker Tools
- Tools For Hacker
- Hacking Tools 2020
- Hack Rom Tools
- Hacking Tools Name
- Hacker Tools List
- Termux Hacking Tools 2019
- Hack Tools For Windows
- Hack Tool Apk No Root
- Hack Tools Github
BEST PASSWORD MANAGERS FOR IOS
BEST PASSWORD MANAGERS FOR IOS
1. ONESAFE PASSWORD MANAGER (CROSS-PLATFORM)
2. SPLASHID SAFE PASSWORD MANAGER (CROSS-PLATFORM)
3. LOGIN BOX PRO PASSWORD MANAGER
Continue reading
- Hack Tools
- Hacker Tools List
- Hack Tools
- Hacker Tools Hardware
- Hacking Tools Free Download
- Hacker Tools For Ios
- Hack Tools For Ubuntu
- Hacker Tools List
- Hacker Tools 2019
- Kik Hack Tools
- Pentest Tools Bluekeep
- Pentest Recon Tools
- What Is Hacking Tools
- Pentest Tools Framework
- Hacking Tools For Windows 7
- Hack App
- Hacking Tools For Games
- Hacking Tools Github
- Hacking Tools Software
- Wifi Hacker Tools For Windows
- Hacking Tools For Beginners
- Hackers Toolbox
- Hacking Apps
- Hack Tools
- Hacking Tools Usb
- Hacking Tools 2020
- Hacking Tools 2019
- Hacking Tools Hardware
- Hacking Tools For Games
- Hacker Tools For Pc
- Hacking App
- Hack Tools For Pc
- Best Hacking Tools 2019
- Tools For Hacker
- Hacking Tools Name
- Hacking Tools For Windows Free Download
- Physical Pentest Tools
- Pentest Tools Github
- Hacker Tools Apk
- Pentest Tools Website
- Hack Tools Online
- Hacks And Tools
- Hacker Tools Software
- Hacker Security Tools
- Hackers Toolbox
- Hack Tools
- Growth Hacker Tools
- Hack Tool Apk No Root
- Hacker Tools 2019
- Nsa Hack Tools
- Hacking Tools For Windows
- Hack Tools For Mac
- Hacker Tools Software
- Hacker Tools 2020
- Hack Website Online Tool
- Computer Hacker
- Physical Pentest Tools
- Hack Rom Tools
- Hacking Tools For Kali Linux
- What Are Hacking Tools
- Bluetooth Hacking Tools Kali
- Hack Tools For Games
- Hacking Apps
- Pentest Tools Github
- Pentest Tools List
- Underground Hacker Sites
- Pentest Tools Port Scanner
- Pentest Tools Linux
- Pentest Tools Find Subdomains
- Hacker Tools Online
- Hack Website Online Tool
- Hacking Apps
- Wifi Hacker Tools For Windows
- Hack Tools
- Pentest Tools Kali Linux
- Hack Tools For Windows
- Hack Tools For Games
- Hack Tools Pc
- Hacker Tools List
- Hack Tool Apk
- Pentest Tools For Android
- Hack Apps
- Blackhat Hacker Tools
- Hacker Tools For Windows
- Hack Tools For Mac
- Pentest Tools Alternative
- What Is Hacking Tools
- Hack Tools Github
- Pentest Tools For Android
- Hack Tools Github
- Pentest Reporting Tools
- Free Pentest Tools For Windows
- Top Pentest Tools
- Hacking Tools Mac
- Beginner Hacker Tools
- Pentest Tools Nmap
- Easy Hack Tools
- Kik Hack Tools
- Pentest Tools Android
- Pentest Tools For Android
- Easy Hack Tools
- Hacking Tools Free Download
- Hack Tools For Ubuntu
- Hacker Tools Windows
- Nsa Hack Tools Download
- Hacker
- Pentest Tools Github
- Pentest Tools Website Vulnerability
- What Is Hacking Tools
- Blackhat Hacker Tools
- Pentest Tools Nmap
- Github Hacking Tools
- Pentest Tools Open Source
- Hacking Tools Online
- Hacker Tools Online
- Hacker Tools Online
- Hacking Tools For Windows
- Hack Tools Download
- Pentest Tools Android
- Pentest Tools Online
- Hacker Security Tools
- Hacking Tools Windows
- Android Hack Tools Github
- Nsa Hack Tools Download
- Pentest Tools Find Subdomains
- Hacking Tools For Beginners
- Hacking Tools For Windows
- Hacking Tools Hardware
- Hacker Tools
- Hacker Tools For Windows
- Hacker Tools Github
- Hacking Tools For Kali Linux
- Hacking Tools 2020
- How To Hack
- Hack Tools For Pc
- Blackhat Hacker Tools
PHoss: A Password Sniffer
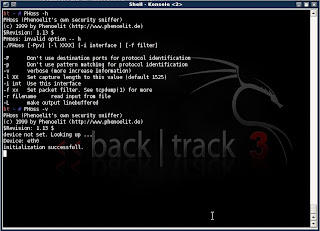 "PHoss is a sniffer. A normal sniffer software is designed to find problems in data communication on the network. PHoss is designed to know some protocols which use (or may use) clear text passwords. Many protocols are designed to use secure authentication. For fallback they define a lowest level of authentication using clear text. Many companies use this lowest fallback definition as standard setting to make the product working in many environments." read more...
"PHoss is a sniffer. A normal sniffer software is designed to find problems in data communication on the network. PHoss is designed to know some protocols which use (or may use) clear text passwords. Many protocols are designed to use secure authentication. For fallback they define a lowest level of authentication using clear text. Many companies use this lowest fallback definition as standard setting to make the product working in many environments." read more...Download: http://www.phenoelit-us.org/phoss/download.html
- Hack Tools Mac
- Pentest Tools Subdomain
- Hack Tools For Ubuntu
- Pentest Tools Nmap
- New Hacker Tools
- Pentest Tools Open Source
- Hacking Tools
- Hack Tools Github
- Hacker
- Wifi Hacker Tools For Windows
- Hacking Tools Windows
- Bluetooth Hacking Tools Kali
- Hacker Tools List
- Bluetooth Hacking Tools Kali
- Tools For Hacker
- Pentest Tools Url Fuzzer
- Tools Used For Hacking
- Hacking Tools For Windows Free Download
- Pentest Tools Url Fuzzer
- Pentest Tools Review
- Hack Tools Online
- Best Pentesting Tools 2018
- Hacking Tools Github
- Hacking App
- Pentest Tools Port Scanner
- Hacker Tool Kit
- Pentest Tools Download
- Hack Tools Online
- Underground Hacker Sites
- Hack Rom Tools
- Hacker Tools Mac
- Underground Hacker Sites
- Bluetooth Hacking Tools Kali
- Hacker Tools For Ios
- Hacker Tools Software
- Hacking App
- Pentest Tools
- Hacking Tools Free Download
- Pentest Tools List
- Hacking Tools Windows 10
- Hacker Tools
- Hack App
- Hack Tools For Windows
- Pentest Tools Framework
- Hacking Tools Free Download
- Hacking Tools For Games
- What Are Hacking Tools
- Pentest Tools For Ubuntu
- Hacker Tools List
- Hacker Tools Apk Download
- Hacker Tools 2019
- Underground Hacker Sites
- Pentest Tools Framework
- Tools For Hacker
- Hack App
- New Hack Tools
- Hacking Tools Mac
- Hacker Tools 2019
- Hacking Tools Windows 10
- Hacker Tool Kit
- Hacking Tools For Mac
- Hackrf Tools
- Pentest Tools Linux
- Hacking Tools Hardware
- Hacker Tools
- Hacker Tools Apk Download
- Pentest Tools
- Pentest Tools Download
- Pentest Tools Website Vulnerability
- Hacker Tools
- Termux Hacking Tools 2019
- Nsa Hacker Tools
- Hack Tool Apk
- Hacking Tools And Software
- Blackhat Hacker Tools
- How To Hack
- How To Make Hacking Tools
- Computer Hacker
- Hacking Tools For Windows Free Download
- Hacker Tools Apk Download
- Pentest Tools Url Fuzzer
- Nsa Hacker Tools
- Hacker Tools Hardware
- Hack Tools Download
- Hacker Tools Linux
- Hack Rom Tools
- Hack Apps
- Hack Tools Online
- Ethical Hacker Tools
- Tools 4 Hack
- Hacking Tools For Games
- Hacking Tools Github
- Hack Tools
- Physical Pentest Tools
- Pentest Tools
- Hack Tools Online
- Hack Tools For Pc
- Hacking Tools Usb
- Pentest Tools For Windows
- How To Make Hacking Tools
- World No 1 Hacker Software
- Hack Tools For Pc
- Pentest Tools Port Scanner
- Hacking Tools Download
- Hacks And Tools
- Hack Tools For Ubuntu
- Hacking Tools Github
- Physical Pentest Tools
- Pentest Tools Online
- Hacking Tools Windows
- Pentest Tools Website Vulnerability
- Hacker Tools Free Download
- New Hack Tools
- Pentest Tools Free
- Hacking Tools Hardware
- Hacking Tools For Games
- Hacker Tools For Ios
- New Hack Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools Find Subdomains
- Physical Pentest Tools
- Hack Tools
- Pentest Tools Website
- Tools 4 Hack
- Hacking Tools
- Hacking Tools Pc
- Hacker Tools Windows
- Hacking Tools 2019
- Hack Tools Mac
- Hacking Tools For Games
- Hacker Tools Apk
- Termux Hacking Tools 2019
- Hacking Tools Pc
- Hacker Hardware Tools
- Hack Tools For Mac
- Termux Hacking Tools 2019
- Hacker Tool Kit
- How To Make Hacking Tools
- Computer Hacker
- Hacker Tools List
- Hacking Tools
- Hacking Tools Usb
- Hack Tools For Mac